Kinsing Miner – how to find and neutralise
-
Published:22 January 2026
-
Updated:21 April 2026

This article is a post‑mortem of the incident that happened to Sequoia in September 2023.
I’m sure that everyone has encountered malware at some point in their lives. Some have lost passwords to phishing sites, others have been targeted by financial fraud, and some suddenly noticed that their phone or computer began to slow down and overheat.
The concept of a "miner" has become one of the most common attack vectors on user devices in the modern world. The ease of mining cryptocurrencies like Monero has allowed attackers to exploit web browsers as a target.
Attackers are also rapidly infecting cloud infrastructure. Poor digital hygiene and vulnerabilities in both open‑source and proprietary tools create fertile ground for the abuse of computing resources.
Metabase and product analytics
For every startup, including Sequoia, it is important to understand what happens inside the product: which features are most popular, how users behave, what actions they perform, and what helps retain the audience.
In the early stages, it is common to use third‑party tools like Firebase Analytics, Amplitude, Yandex AppMetrica, and others.
However, for tasks requiring direct access to the primary database, these tools are not suitable. Often, startups use open‑source or self‑hosted solutions. One of the well‑known, popular, and flexible tools is Metabase.
For Sequoia, it proved that we can build any dashboards and charts that were impossible to create with third‑party cloud services.
Miner detection
Infrastructure monitoring is a critical part of DevOps culture. When processes are built correctly and competently, it becomes normal to quickly detect and prevent threats.
During our weekly review, we noticed that one of the Docker machines started consuming abnormally high amounts of CPU and RAM.
The first step was to analyze the processes by CPU consumption to determine which one was out of the norm.
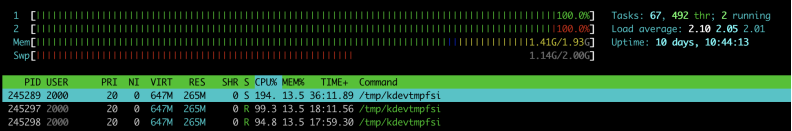
We detected the process kdevtmpfsi. A quick search shows that it is a well‑known malware miner.
The source of the problem
After removing the miner and its files and blocking outgoing ports, we needed to determine how it got into the system. Initially, our cloud infrastructure blocked access to the machine (except HTTP(S) and SSH).
To understand who actually initiated this process, it is necessary to consult the process tree, which reveals the initiator behind the launch of a specific program – whether it be the system, a user, or another program.
Analysis of the process tree revealed that the miner was not located on the host machine but inside an active Docker container.

The next step was to identify the Docker image the miner was running in. To do this, we examined the path to the executable file.
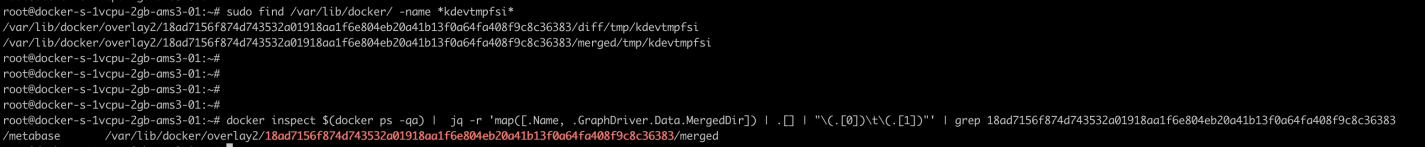

It turned out that the miner was running inside a Metabase container — the product analytics tool we use at Sequoia.
Reason for appearance
The self‑hosted version of Metabase installed on Sequoia’s servers contained a vulnerability that allowed an attacker to connect to the machine and execute arbitrary commands. The miner was installed through this vulnerability.
A detailed analysis of the vulnerability was published on the Metabase blog: https://www.metabase.com/blog/vulnerability-post-mortem
Consequences
In Sequoia's case, user data was not affected. However, the infrastructure was disrupted for several days, resulting in decreased API response time.
We updated self‑hosted tools, changed infrastructure configuration, and reviewed security policies — all without harming user experience or data.
Tips for the Future
I would advise our readers to pay closer attention to the frequency and tools used for their security audits. Review all dependencies and reduce their number to minimize their impact on your infrastructure. And always isolate user data to minimize both technological and reputational risks.
Best,
Aliaksei Saskevich
CTO Sequoia





.svg)
.svg)
